Two-factor authentication (2FA) is one of the most effective ways to protect accounts from phishing, password leaks, and unauthorized access.
Almost every Internet user has encountered two-factor authentication (2FA) at least once — when logging into online banking, corporate systems, email accounts, cloud services, or even social media. However, not everyone clearly understands how it actually works.
Two-factor authentication adds an additional security layer to a standard login and password. Instead of relying on just one piece of information, the system verifies the user using two independent factors. This significantly reduces the risk of unauthorized access.
Let’s take a closer look at how 2FA works and where modern solutions such as Protectimus fit into this process.
What Is Two-Factor Authentication (2FA)?
Two-factor authentication (2FA) is a security mechanism that requires users to verify their identity using two different authentication factors before gaining access to an account or system.
Typically, these factors include:
- a password or PIN (something the user knows)
- a device that generates a one-time password or receives a login confirmation (something the user has)
This additional verification step significantly reduces the risk of unauthorized access, even if the password becomes compromised.
The First Factor – Something You Know
The first authentication factor is usually the standard password used to log in to a website or system.
This is known as a knowledge factor because it relies on information that only the user should know. Other examples of knowledge factors include:
- PIN codes
- security questions
- passphrases
However, passwords alone are not reliable protection. They can be:
- stolen in phishing attacks
- leaked in database breaches
- guessed or reused across multiple services
This is why modern security systems combine passwords with an additional authentication factor. You can also read our guide What Is Two-Factor Authentication? for a broader overview.
The Three Authentication Factors
Authentication mechanisms are traditionally divided into three categories:
- Something you know — password or PIN
- Something you have — token, smartphone, smart card
- Something you are — biometric characteristics
Two-factor authentication combines any two of these factors.
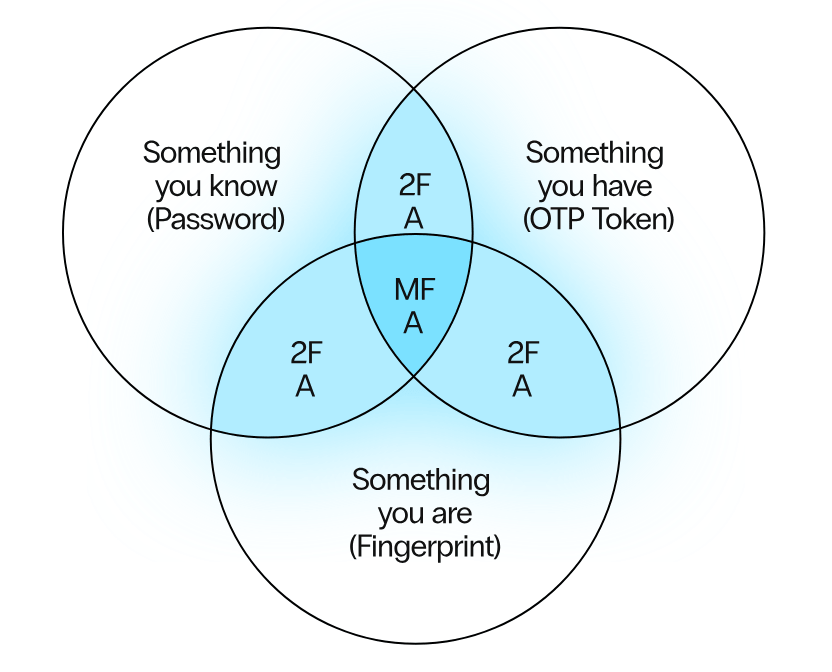
What Is the Difference Between 2FA and MFA?
Two-factor authentication (2FA) is a subset of multi-factor authentication (MFA).
The difference is simple:
- 2FA uses exactly two authentication factors.
- MFA can use two or more authentication factors.
Most modern security systems, including the Protectimus MFA platform, support multiple authentication methods and allow administrators to configure flexible authentication policies.
How 2FA Works – A Simple Example
Typical two-factor authentication process:
- User enters login and password
First authentication factor — something the user knows. - The system requests a one-time password (OTP)
The authentication server generates or requests a temporary verification code. - User enters the OTP or confirms login
The code is generated by a hardware token, authenticator app, or delivered via chatbot, SMS, or email. - Access is granted
If both factors are valid, the user successfully logs in.
Modern authentication platforms like Protectimus MFA manage this entire process — generating OTP codes, delivering them to users, and verifying them during authentication.
The Second Factor – Something You Have
The most common second factor today is a device that generates or receives one-time passwords (OTP).
This can include:
- hardware OTP tokens
- mobile authenticator apps
- SMS or email OTP delivery
- push authentication
- messenger chatbot OTP delivery
The Protectimus MFA platform supports multiple authentication methods:
- Hardware OTP tokens — dedicated devices that generate secure one-time codes;
- Protectimus SMART — a mobile authenticator app for generating OTP codes;
- OTP delivery via chatbots — secure delivery through messengers such as Telegram and Viber;
- push, SMS, or email OTP delivery.
This flexibility allows organizations to choose the most convenient authentication method for different user groups and use cases.
Biometric Authentication – Something You Are
Biometric authentication relies on unique physical characteristics of the user.
Common biometric factors include:
- fingerprint
- face recognition
- voice recognition
- iris or retina scan
Biometrics are widely used for device unlocking and physical access control. However, they are less common for remote authentication in corporate systems because biometric data cannot be changed if compromised.
For remote access security, OTP-based authentication remains one of the most reliable approaches.
How One-Time Passwords Are Delivered
One-time passwords are valid only for a short time and can be used only once. Even if intercepted, they become useless after expiration.
OTP codes can be delivered to the user in several ways:
- SMS messages
- mobile authenticator apps
- push notifications
- hardware tokens
- messenger chatbots
Protectimus supports all these methods, including mobile OTP generation, hardware tokens, chatbot-based OTP delivery, push, SMS, and email OTP delivery, helping organizations balance security, convenience, and cost.
Comparison of Popular Two-Factor Authentication Methods
| Method | Security Level | Convenience | Example |
|---|---|---|---|
| SMS OTP | Medium | Very easy | Code sent via SMS |
| Email OTP | Medium | Easy | Code sent by email |
| Authenticator App | High | Convenient | Protectimus SMART |
| Hardware Token | Very high | Requires a device | Protectimus hardware tokens |
| Messenger Chatbot OTP | High | Very convenient | Protectimus chatbot OTP delivery |
Different authentication methods offer different levels of security and convenience. Many organizations choose flexible MFA platforms such as Protectimus that support several authentication options simultaneously.
How OTP Codes Are Generated
Most modern authentication systems use standardized algorithms defined by the OATH Initiative.
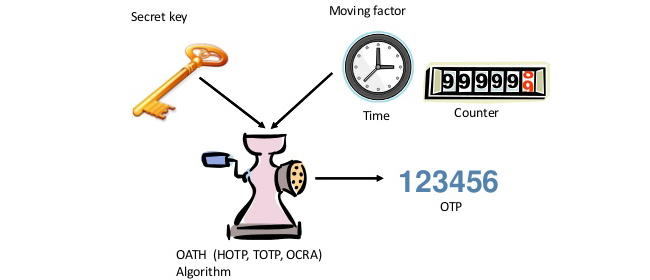
HOTP – HMAC-Based One-Time Password Algorithm
This algorithm generates passwords based on a counter value and a secret key shared between the user and the server. It is suitable for scenarios where event-based code generation is required.
TOTP – Time-Based One-Time Password Algorithm
TOTP is currently the most widely used OTP algorithm. It generates a new code every fixed time interval, usually every 30 seconds.
This is the algorithm used by most authenticator apps, including Protectimus SMART. You can also learn more in our article TOTP vs HOTP: What’s the Difference?.
OCRA – OATH Challenge-Response Algorithm
OCRA generates one-time passwords using a server challenge and can support transaction signing with the Confirm What You See (CWYS) principle. This makes it especially suitable for banking systems and other high-security environments.
Unlike HOTP and TOTP, which are typically used for one-way authentication, OCRA can also support mutual authentication and more advanced verification scenarios.
Why Two-Factor Authentication Is So Effective
The strength of 2FA lies in combining two independent factors.
Even if an attacker steals a user’s password, they still cannot access the account without the second authentication factor.
Similarly, stealing a token or intercepting an OTP code alone is not enough without the password or another knowledge factor.
This layered approach significantly increases account security and makes two-factor authentication one of the most effective protection methods available today.
Is Two-Factor Authentication Safe?
Yes. Two-factor authentication dramatically improves account security because it requires two independent verification factors.
Even if attackers obtain a user’s password through phishing, malware, or data breaches, they still cannot access the account without the second authentication factor.
Using stronger second factors such as hardware OTP tokens or authenticator apps like Protectimus SMART further increases protection against phishing and unauthorized access.
Frequently Asked Questions About Two-Factor Authentication
What is two-factor authentication?
Two-factor authentication (2FA) is a security method that requires users to verify their identity using two different authentication factors — typically a password and a one-time password.
Why is 2FA more secure than passwords alone?
Even if an attacker steals a password, they still cannot access the account without the second authentication factor, such as an OTP code, hardware token, or authenticator app.
What devices can generate one-time passwords?
OTP codes can be generated by hardware tokens, mobile authenticator apps like Protectimus SMART, or delivered via SMS, email, or secure chatbots.
Is biometric authentication part of 2FA?
Yes. Biometrics such as fingerprints or face recognition can be used as one of the authentication factors, typically combined with a password or device.
What is the difference between TOTP and HOTP?
TOTP generates codes based on time intervals, while HOTP generates codes based on a counter value. TOTP is the most commonly used algorithm in modern authenticator apps.
Looking to Implement Two-Factor Authentication?
The Protectimus MFA solution allows you to deploy secure authentication using: quickly
- mobile authenticator apps
- hardware OTP tokens
- SMS or email OTP
- secure chatbot OTP delivery
Explore the available authentication options on the Protectimus Tokens page.
Subscribe To Our Newsletter
Join our mailing list to receive the latest news and updates from our team.

Subscribe To Our Newsletter
Join our mailing list to receive the latest news and updates from Protectimus blog.
You have successfully subscribed!